Social Engineers Spoof Corporate Security at DEFCON 25 Hacking CTF
Las Vegas, NV – Ever since DEFCON 18, there has been a village within the conference dedicated to the art of human hacking, also known as Social Engineering. By the village’s definition, social engineering is “any act that influences a person to take an action that may or may not be in their best interest”. This year, SEVillage not only hosted the Social-Engineer Capture The Flag (SECTF), but also SECTF4Kids, SECTF4Teens and Mission SE Impossible.
Our research shows that the exact same principles that are used to get a raise or communicate with your spouse or children are often used by malicious scammers and social engineers to part you and your company from data, information, money and more.” – SEVillage
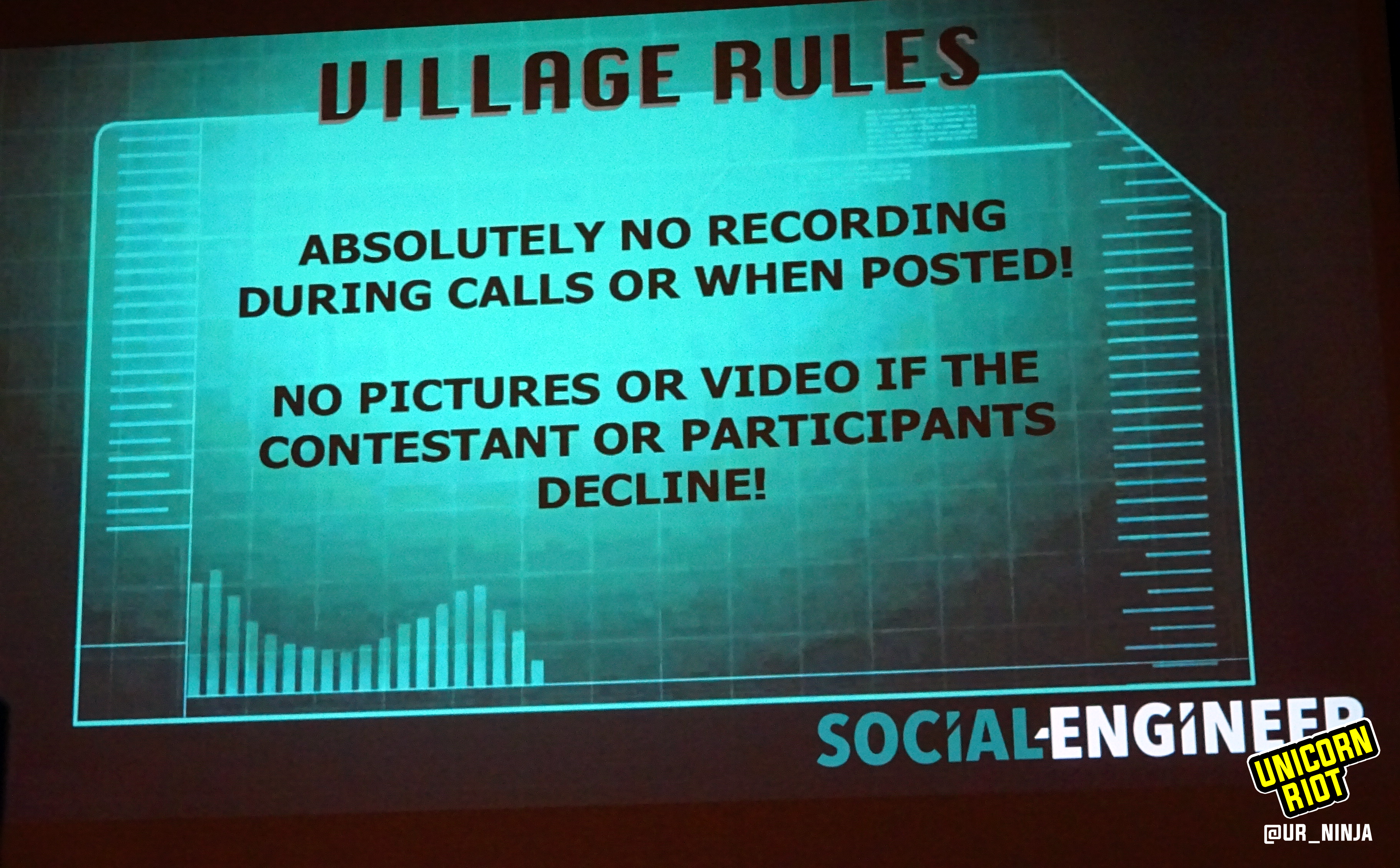
We entered the village which was arranged with audience seating and a stage. Atop the stage was a panel of experts to keep track of the score, set up the spoof number, and dial out. The stage also hosted a small sound proof booth containing a chair and a microphone, with a clear front panel so that the audience could observe. No one was allowed to make audio or video recordings of the “Phone Calls”. Therefore, we will describe a few of the calls we experienced.
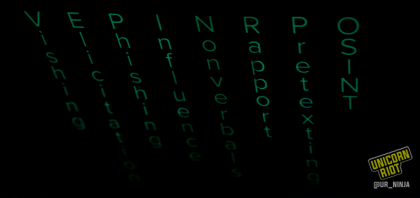
Pretexting: Using false pretenses, the callers obtain company information from employees that can lead to exploitation of company information.
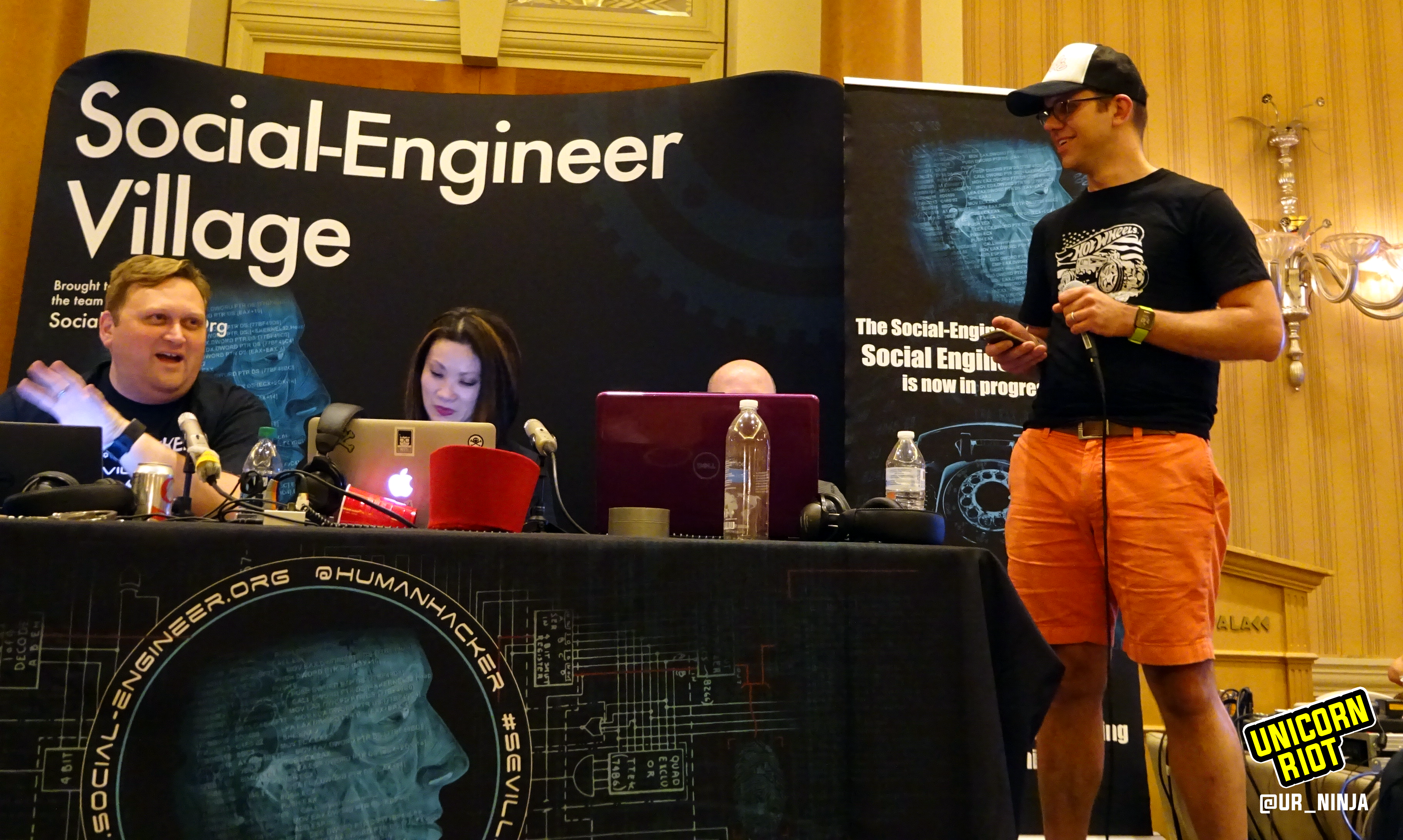
Each contestant wore headphones, gripped their scripts of pretext, and spoke into the microphone. Both lines of the call, sender and receiver, were broadcast out to the audience via speakers. Next to the stage, a video screened a closer look at the contestant for the rear of the audience, and displayed relevant memes and pictures that went along with the content of the calls.
Vishing: The practice of eliciting information or attempting to influence action via the telephone, may include such tools as “phone spoofing.”
When the caller was ready, the judge closest to the booth operated a switchboard to dial calls out. Together they took notes, relayed messages silently with body language, and conferred amongst themselves and with the caller about the CTF rules. The audience sat eager to witness the expertise of the these social engineers, see them score points, and celebrate both the wins and the fails as learning experiences. Because of this excitement, the judges frequently shushed the crowd, lest they be heard by the receiver of the call.

CALLER #1
The caller enters the soundproof room and the crowd begins to settle into their chairs. At this point the spoof number is set up. Spoofing is when hackers “cause the telephone network to indicate to the receiver of a call that the originator of the call is a station other than the true originating station” on the receiver’s phone’s ‘caller ID’. The judge sets the 20 minute timer on display in the front of the room. Looking over at the caller the judge asks, “You ready?”. The crowd is silent. The caller gives the thumbs up, the timer begins running, and a number is dialed.
Through the PA system at the front of the room a voice projects, “Hello?”
Caller: “Is your store open? There’s some network disruption. Can you help me?”
Manager: “Yea what do you wanna know?”
Caller: “Are you in front of a computer?”
Manager: “Yea but i don’t really know what I’m doing.”
The crowd giggles and nudges each other in their chairs.
Caller: “No problem do you have a browser?”
Manager: “Yes. ******** is open right now.”
Caller: “Ok, just type the in the following URL: SEORG.org.”
Manager: Typing…..
Caller: “Does anything come up?”
Little does the store manager know that the website he just entered led directly to the social engineering splash page for the exact SEVillage CTF competition that was going on in the room. The website read:
“This truly unique event will challenge you and test your abilities to use social engineering skills to gather small amounts of data from unsuspecting companies over the phone. Each contestant will be assigned a target company. WHO IS THE SOCIAL ENGINEER CHAMPION?”
The crowd begins laughing uncontrollably, audibly louder than the social engineering wizardry they were watching unfold in front of them. The judges shush them, waving with both hands, and a message is put on the screen to please remain quiet.
Manager: “Yes I’m getting internet without any issue.”
Caller: “Seorg.org, what does it say?”
Manager: “It says…social…..engineer….”
Caller: “Oh, that seems wrong, there’s clearly something wrong with your network. Go to thismachine.info.”
Manager: “Ok. It says what browser am I using. It shows ******* version ***************************.”
Just as the manager starts reading his IP address to the the caller (and the audience), the judges cut the audio out, sparing the company on the phone from giving away their critical data to a room of hackers. *Note that the caller did not ask for the IP address, but the manager on the phone was so willing to help that he simply gave it to the caller.
At this point the crowd was practically falling on the floor in laughter.

Caller: “Click on all programs. Do you see anything like Cisco?”
Manager: “No.”
Caller: “What about Airwatch? Maybe VMWare?”
Manager: “No.”
Caller: “By the way, your on a ******* computer correct?”
Manager: “Yes.”
Caller: “Laptop or desktop?”
Manager: “Desktop. The only laptop we have is back in the IT closet.”
Once again the crowd bursts out into laughter.
Caller: “How long you been working for [Gaming Company]?
Manager: “Going on four years.”
Caller: “Do you have cell phones?”
Manager: “Yea.”
Caller: “What type?”
Manager: “It says ****** phone.”
The crowd roared in laughter and was promptly shushed.
Manager: “We had this problem last week with credit cards. Not surprised something is wrong with it again.”
Caller: “Do you have badges?”
Manager: “Yea, to get in and out.”
Caller: “Any problems?”
Manager: “No, that works fine.”
Caller: “Is your card thin HID or thicker like RFID?”
The manager asks another employee what type of badges they use. He comes back to the phone to tell the caller.
Caller: “Ok I’m going to send you a new router… What shipping company do you use?”
Manager: “Im gonna set up the router and use ******* as ID for registered devices.”
Caller: “Very good.”
Manager: “Yea we should be safe. All the routers are in the IT closet.”
Crowd begins laughing, still reeling from the last breach.
Caller: “Who does your trash?”
Manager: ….silence….
Caller: “Great, what time do you close?”
Manager: “9PM tonight!”
Caller: “If theres any trouble can i send you a PDF instruction?”
Manager: “Yea, my email is *********************.”
The person behind the curtain mutes the personal info from being broadcast to the audience in realtime.
Caller: “Could you open Adobe and let me know what version it is?”
Manager: “Sure.”
(Crowd laughing)
Manager: “Version 2017-**************.”
Caller: “And you have Outlook to receive that?”
Manager: “Yea.”
Caller: “One more question.”
Manager: “Yea.”
Caller: “We wanna make sure your McAfee Antivirus is also is up to date with the latest patches.”
Manager: “Yea it seems updated.”
Caller: “When was last time you had awareness training?”
Manager: “I’m not sure… Last year maybe.”
Caller: “Ok great. I’ll send out that email later today, thanks!”
— end of call —
Seven of the twenty minutes still remain on the clock. Everyone in the audience shoots out of the their chairs in applause. The speed of this caller was incredible, he was very precise and convincing. There was still time to make another call from the list of possible recipients which the caller had prepared beforehand.
Caller: “Hi, i just got a page saying your system is down?”
Manager: “I just got here and everything seems good.”
Caller: “Weird. I need to leave the office in a minute. Can you help me?’
Manager: “Sure how do I do that?
Caller: “Are you using a browser like ********?”
Manager: “Yes.”
Caller: “I need you to connect to back-end systems. Type ************************…Thanks so much.”
Caller: “…See anything?”
Manager: “No, I don’t see anything…”
Caller: “I want to make sure your internet is working. Can you try going to Facebook?”
Manager: “Ok… Yea.”
Caller: “Thats working? Great. So it’s just a problem between corporate and store… Can you type in Seorg.org?”
Manager: “Yea.”
Manager: “No, its telling me it’s a weird page.”
Caller: “We should have this up and running in a second…Type thismachine.info…”
Manager: Typing…
(crowd laughing)
Caller: “Thanks so much. I really appreciate it.”
Caller: “So what browser does it say?”
— the twenty minute timer goes off, ending the CTF round —
The caller walks out of the sound-proof box and before hundreds of people standing in ovation. This caller earned themselves a Black Badge from DEFCON as recognition of their ‘1337 skillz’, and giving them lifetime entry into DEFCON.

CALLER #2
A robotic old wizard voice answers and begins speaking: “Hello my friend, thank you for calling [Gaming Company]. If you know the extension of the brave adventurer your trying to reach please enter it now.”
The crowd begins laughing uncontrollably trying desperately to stop as the judges quickly gesture for silence. A number is then entered into the calling system. Medieval guitar music strums through the speakers as the caller is being transferred, as if patiently waiting through a loading scene of the video game Diablo.
The crowd, on the edge of their seats, giggled and shushed as they gazed forward at the caller. The caller sat alone, wearing headphones near a microphone, closed off in a soundproof room. He sat quietly actively reviewing notes on a laptop, listening and waiting for a human to pick up the phone.
Unfortunately, it was a Friday during lunch and many employees were not at their desks. Time after time the receptionist with the company transferred the caller to various people on the social engineers list of targets. Towards the end of the CTF round, the caller began desperately requesting to speak to anything, preferably an intern, before the time ran out. Each time the caller was transferred by reception the crowd giggled as the robotic wizard began speaking…”Hello my friend…”
To no avail, the social engineer was unable to get through to any human outside the reception desk. As the end of the CTF round drew near, the caller quickly began asking questions to reception. To the surprise of the judges and audience, the reception desk stated that they were unable to divulge company info.
— the twenty minute timer goes off, ending the CTF round —

CALLER #3
The caller, pretending to be journalist writing story about [Gaming Company] fandom, dials in from behind the soundproof booth. Reception answers and the social engineering caller requests to be transferred to a specific person in the office, which they had gathered through OSINT prior to the competition.
Reception: “Let me check with the team to make sure it is OK.”
The caller is put on hold and some modern variant of Shinobi theme music begins playing in the background.
Back on the phone, an employee picks up from some unknown department, this time inquiring for more details.
The caller speaks to employee on the other end of the phone saying she’s already got most of the big interview questions answered and she just needs a few small “fluff” questions answered, perhaps something the they could do. The employee put the caller on hold and confers with their team.
Employee: “************ said you probably need to speak to the other team.”
Caller: “Do you have Chrome? Can you open Chrome and type in URL?” ************ said the questions were hosted at this URL.”
The employee then stated they need it emailed to their team and couldn’t type it in, and would also need to forward the information to the proper team. The caller then asked if the employee was using Mac or PC, as well as if they were “using Chrome, or something?”.
By the time the CTF timer ran down, the caller had gathered multiple flags but not enough to win first place. During the Q & A afterward, the caller stated they had discovered the email address and name of real reporter using open-source intelligence gathering (OSINT), which was a very common way social engineers hack humans.

CALLER #4
The phone rings and after a beat, cue the typical smooth jazz elevator music. Another man at the help desk answers in San Francisco.
Caller: “Hey, I work over in the Sydney branch, looking to get some IT support, can you transfer me to the help desk?”
Receptionist transfers him. The call goes to voicemail.
The caller tells the person operating the call board to cut the line and redial front receptionist again. The receptionist picks up.
Caller: “Hi, this is Edward again, I just called a bit ago. I got a voicemail, is there someone else in the office that could help me?”
Receptionist agrees, dials another employee. The caller gets voicemail again. SEVillage operator cuts the line, redials again.
Caller: “Hi, sorry, again I got voicemail…”
Receptionist: “Oh sorry about that, hold tight for a minute. Let me try to find somebody.”
The caller waits on hold for about 2 minutes. His 20 minute time limit in which he can capture flags and win this game is slipping away.
Receptionist: “It seems everyone is out to lunch, would you like to be transferred to the Montreal office?…”
The caller looked over at the dial out operator at the booth, who was shaking his head and signaling not to transfer out to Canada (for legal reasons).
The caller refused the offer to transfer to Canada which prompted the receptionist to offer a toll free support number as his final solution.
Caller: “Ok, I’ll try that. Hey, by the way, does your company have RFID or HID badges to get around in the office?”
Receptionist says he doesn’t know. The caller describes the differences, explaining that went he visits he wants to know if his key will work. The receptionist is very agreeable and looks, but says he doesn’t know.
At this point, it doesn’t appear that the caller has scored any flags in the live phone call portion of the game. The caller asks for the office administrator and the receptionists replies that they are also at lunch. The caller asks if they have a cafeteria at their workplace. The receptionist might have let on at this point if there was a cafeteria or not. Then the call was ended. The audience was laughed and had to be shushed before the dialer at the table next to the sound booth called the toll free number.
The robotic voice that answered said “Press 2 for VPN access”, which sent the crowd into laughter again. This was a bit of a trail off, and when prompted for a code, they cut the call and dialed the receptionist in San Francisco again.
The caller asked the receptionist again for help, asking when he could call, when the office was open, what hours the IT team usually worked and the receptionist tried again to transfer him, but he hit a voicemail and the 20 minute buzzer sounded.
In a ten minute Q&A session after the call, one of the judges explained that they were not able to transfer the call to Canada during the game, as their lawyers only covered businesses within the US. To make the call seem more real, they had “spoofed” the number to appear that it was coming from Australia.

CALLER #5
The next contestant in SECTF was a younger man with long hair. He had a few numbers to dial that were prepared on paper which he handed to the judge. When the first person he called answered, he used the pretext that he was with a sanitation company and wanted to know who the company currently uses. The person said that he didn’t know.
In another call, he asked someone else to help him close a help ticket, but the person answered that they weren’t by a computer.
Finally he calls another and chats with them about their vending machines. He asks who services them, saying he has a superior product. When the person on the other end admit that their vending machines are subsidized, he follows closely with his pretext and says that might not be a good fit for business.
By the time the buzzer sounded, he had not appeared to get many flags.

Contestants registered with SEVillage prior to DEFCON in order to compete in the SECTF (social engineering capture the flag). Following acceptance to the competition, they were only given a limited amount of time to research their assigned targets. The information contestants used to woo flags from their targets had to be found using only open-source information such as Google, LinkedIn, Instagram, Facebook, Twitter, and Wikileaks. The Electronic Frontier Foundation (EFF) has assisted SECTF from the first year and every year since to ensure they stay within legal boundaries while eliciting flags.
This is the coveted #DEFCON ‘black badge’, given to the ‘best of the best’ hackers who competed in various tasks at #defcon25 conference pic.twitter.com/n6ILxe9c6v
— Unicorn Riot (@UR_Ninja) July 31, 2017
To learn more about Social Engineering, see the SEVillage Framework for more definitions and real life examples.
To help our volunteer-operated, horizontally-organized, non-profit media collective please consider a tax-deductible donation: