Pwning Targets Through Social Engineering at DEFCON
Las Vegas, NV – Social engineering (SE) is defined as “any act that influences a person to take an action that may or may not be in their best interest”, according to the website social-engineer.org.
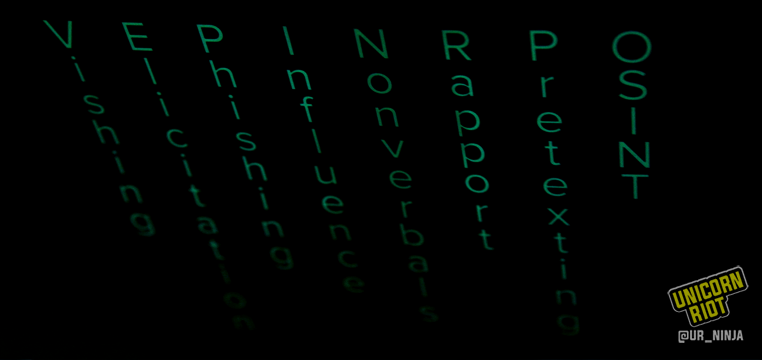
The art of social engineering can be used for a wide variety of purposes, from hunting pedophiles, to gaining access to Fortune 500 companies, and even stealing secure data. Social engineers use a variety of methods to compromise their target, including phishing, Vishing, SMishing, and impersonation.
Social Engineers have an arsenal of psychological and physical tools to gather intelligence during reconassaince before laying the pwn down on their targets. Open Source Intelligence (OSINT) can be one of the greatest resources to create models and track the target. Some of the easiest places to start gathering intelligence on people and companies are publicaly assesible such as social media profiles and websites. More dirty methods for gathering intelligence include sometimes diving into a dumpster and searching through trash for phone numbers and email addresses.
Computer based software such as Maltego allows the SE to mine information and identify key relationships to exploit. The social engineer toolkit application allows advanced customization to pentest exploits. The software allows users to spoof email addresses, carry out spear-phishing and mass mailing attacks, create a payload listener, SMS spoofing, and more.
Psychology also plays an important role in exploiting and compromising your target. Commonly used methods are observing and exploiting micro-expressions, developing instant rapport with individuals, interrogation/interviewing your target, getting the targets mind to “buffer overflow”, and even neuro-linguistic programming (NLP).
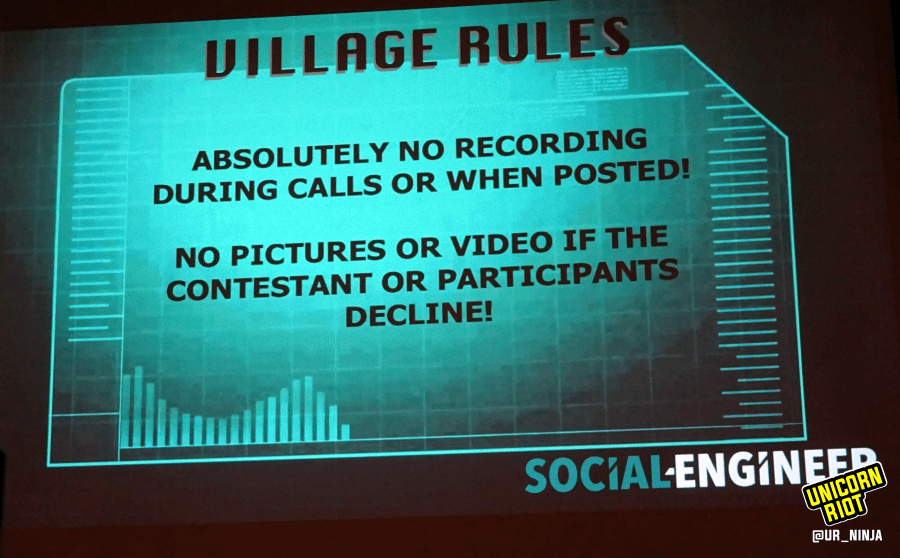
We interviewed Chris from the Social Engineering Village at DEFCON 26, in Las Vegas, to find out more.
Read our detailed report from last years live capture the flag (CTF) social engineering competition at DEFCON 25.
Social Engineers Spoof Corporate Security at DEFCON 25 Hacking CTF
Please consider a tax-deductible donation to help sustain our horizontally-organized, non-profit media organization:

Written by Andrew Neef & Rachel Weiland