Hacking LIDAR: Changing What Autonomous Vehicles See
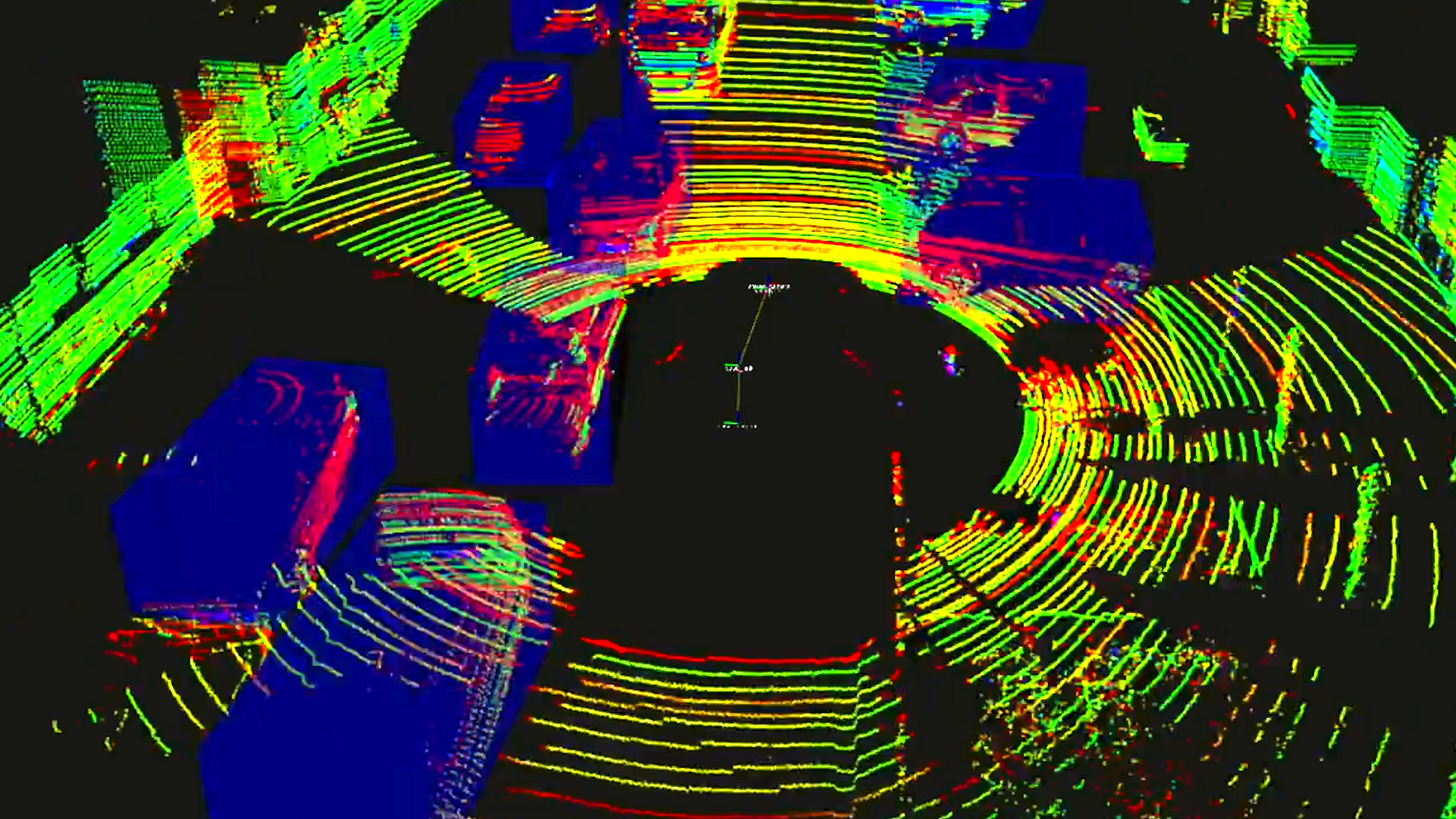
Las Vegas, NV – In the near future, automobile manufacturers are expected to begin rolling out autonomous driving vehicles that use Light Detection and Ranging (LIDAR) lasers to see objects, roads, and people.
These driver-less vehicles will soon be cruising down every major city street, through school zones and storms, and even delivering you pizza. But what if, for example, your autonomous pizza delivery vehicle doesn’t see a pile of trash that blew over into the road?
At DEFCON 27 hacking conference in Las Vegas, Unicorn Riot spoke with Dr. Richard Hansen, who partnered with Hawk Security to investigate ways in which LIDAR could be disrupted in autonomous driving vehicles. During the testing phase, the group only used everyday household items which can be easily obtained at your local hardware or grocery store.
“We tried to see if we could sow chaos for a few dollars.” – Dr. Richard Hansen
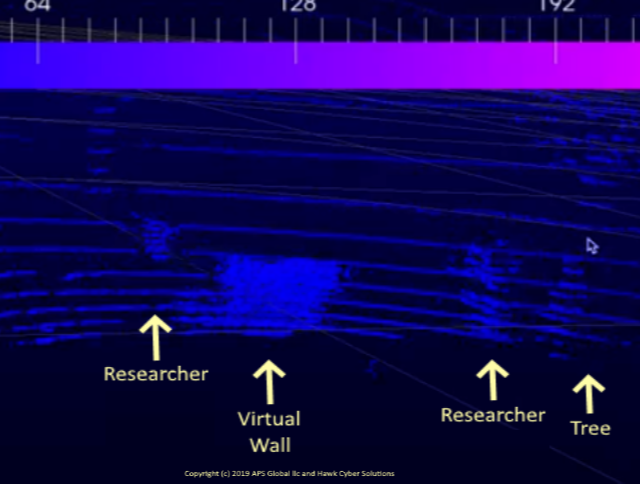
According to Dr. Hansen, experiments using just a black trash bag appeared to be the most effective method of obfuscating an object that the LIDAR detects which is actually there. The trash-bag works much like an F-117 Stealth Bomber because it deflects and absorbs the wavelengths which the LIDAR lasers use to survey an area.
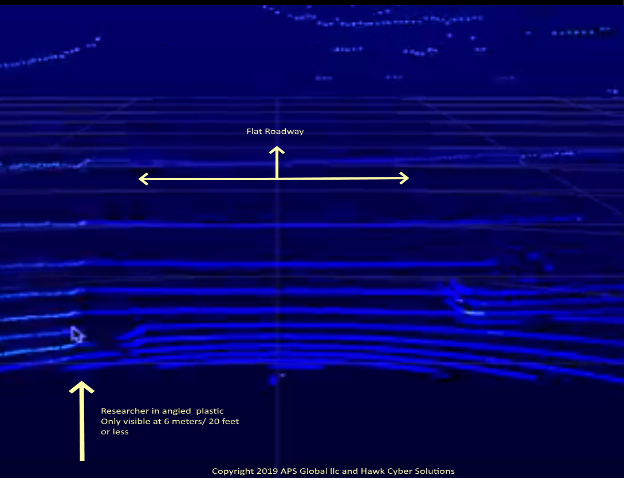
The group of hackers also found that the LIDAR lasers would interpret a particular mixture of powders as a sort of wall. According to Dr. Hansen, the powder was able to be suspended for up to 30+ seconds, long enough to bring a car to a stop.
This may sound like the work of a mad scientist hell-bent on sowing chaos for autonomous pizza delivery vehicles but the reality is far less exciting (though perhaps much better for your driver-less taxi experience). Dr. Hansen hacks technology such as LIDAR for a living, identifies vulnerabilities, and works within the industry to make autonomous vehicles safer in the future.
Dr. Hansen also stresses that anyone wishing to conduct similar tests should:
“Be careful not to get anyone run over or blown up in the process.” – Dr. Hansen
Please consider a tax-deductible donation to help sustain our horizontally-organized, non-profit media organization:

Follow us on Twitter, Facebook, Youtube, Vimeo, Instagram, and Patreon.
Unicorn Riot's DEFCON Coverage:
- Social Engineers Spoof Corporate Security at DEFCON 25 Hacking CTF
- Hacking Drones With Ultrasonic Pulses at DEFCON
- Hacking Drones at DEFCON: “All Skyz Belong To Us”
- Winn Schwartau Discusses Cyber Security at DEFCON
- Pwning Targets Through Social Engineering at DEFCON
- Queercon Brings Together LGBTQ InfoSec Community at DEFCON
- Cryptocurrency & Blockchain Gain Momentum at DEFCON
- Sex Work After SESTA/FOSTA: A Discussion With Maggie Mayhem at DEFCON
- Hackers Discover Chinese Music Hidden in US Voting Machine Software
- “You Are The Product”: Big Data & Social Media Safety